Learning from the Mistakes of Others: The Snowden Incident
By: Nextech | February 13th, 2015

Part 2: The Snowden Incident
In Silicon Valley today, President Obama is hosting a White House summit on Cybersecurity. A gathering of top tech experts will be there to give lectures and provide input on the subject, including Apple CEO Tim Cook. However, a large number of the best-known senior tech executives will be notably absent from the summit—Mark Zuckerberg (Facebook), Marissa Mayer (Yahoo), Larry Page (Google), Eric Schmidt (Google), and even Bill Gates (Microsoft) all chose to decline their invitations. All of them sent corporate information security officers to attend in their steads.
One has to admit, it seems odd to have a summit of this type without them.
 Their decisions not to attend the summit, many have speculated, may have something to do with the disclosure of the NSA’s “Prism effort” surveillance program, one of many secret programs uncovered by Edward Snowden’s breach of the National Security Agency. A report published barely a year ago by the Guardian revealed that “Tens of thousands of accounts associated with customers of Microsoft, Google, Facebook, and Yahoo have their data turned over to US government authorities every six months.” This damaged their brand reputations, and executives from all four groups have been doing their best to publically distance themselves from the U.S. government, hoping to assure their customers that their privacy will remain secure against what some view as unnecessary government snooping. Interestingly enough, many view Edward Snowden’s breach of the NSA as a catalyst to the U.S. government finally taking a serious position on cybersecurity.
Their decisions not to attend the summit, many have speculated, may have something to do with the disclosure of the NSA’s “Prism effort” surveillance program, one of many secret programs uncovered by Edward Snowden’s breach of the National Security Agency. A report published barely a year ago by the Guardian revealed that “Tens of thousands of accounts associated with customers of Microsoft, Google, Facebook, and Yahoo have their data turned over to US government authorities every six months.” This damaged their brand reputations, and executives from all four groups have been doing their best to publically distance themselves from the U.S. government, hoping to assure their customers that their privacy will remain secure against what some view as unnecessary government snooping. Interestingly enough, many view Edward Snowden’s breach of the NSA as a catalyst to the U.S. government finally taking a serious position on cybersecurity.
The Snowden Incident
In part 1, we talked about the Sony Pictures hack, which was ultimately the work of spear-fishing, but there is a much simpler way to gain private information. Which brings us to Edward Snowden (remember him?). While the NSA has done its best to paint Snowden as a slacker who just got lucky, this portrayal does not seem entirely accurate by other accounts. The truth is that Snowden is highly intelligent (IQ 145), with military training (he was discharged after breaking both legs in a Special Forces training accident). He also formerly worked for the Global Communications Division of the CIA. At the time of the NSA breach, Snowden was working for a private tech consulting firm, Booz Allen Hamilton, and was assigned as a computer systems administrator (but still as an outside, private contractor) for the NSA Regional Operations Center in Hawaii.
While Snowden used his intelligence and computer skills to locate classified data and cover his tracks, he didn’t need either of these attributes to actually access them. In fact, if one want to get technical about it, he didn’t actually “Hack” the NSA network. So… what did he do? Perhaps it might be best to explain this in the form of a joke:
How do you get a bunch of NSA agents to tell you their secure network password?
You just ask them for it.
I know… it’s not funny. And it shouldn’t be.
I wish I was exaggerating or making this up, but I'm not. The scary truth is that Edward Snowden was able to gain access to some of the NSA’s most top secret, classified documents (as well as some from the British GCH) by simply asking agents for their passwords. It was reported by Reuters that Snowden was able to convince “between 20 and 25 fellow workers at the NSA … to give him their logins and passwords by telling them they were needed for him to do his job as a computer systems administrator.” In the agents’ defense, it seems there was no clear NSA policy at the time about internal password sharing. They may not have realized that they were doing anything wrong. After all, working at the NSA requires security clearance. So they may have believed they were sharing their credentials with an authorized individual.
Once Snowden had these credentials, of course, he had to use far more complex methods to avoid detection as he removed the data (which also gave himself enough time to flee the country). However, if those NSA agents had not freely handed him the “keys to the kingdom,” so to speak, Snowden wouldn’t have been able to access and copy the data in the first place. Sure, he might’ve known where the data was located… but, without the necessary login credentials, he never would have been able to access it without being detected.
Snowden’s breach of the NSA is a perfect, though perhaps extreme, example of what can happen when an organization does not implement a clear and strict policy regarding the creation and sharing of passwords.
Is Password Security the Chink in Your Network’s Armor?
When it comes to cybersecurity, passwords are often the first line of defense. Unfortunately, password security is frequently compromised by users in three main ways—(1) failing to create unique passwords, (2) password sharing, and (3) not regularly changing passwords. By examining the various password mistakes that many users make, you will be better prepared to avoid them.
1. Unique Passwords
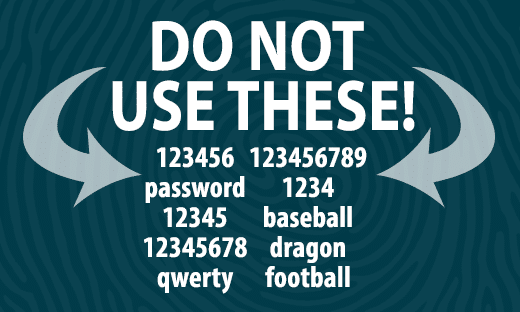
Creating unique and strong passwords is an important part of any network’s security. Start by making sure that everyone on your staff knows the Top 25 List of Common Passwords, and make it clear to them that these passwords are not to be used for office purposes. The reason for this is pretty simple—almost any hacker trying to gain unauthorized access to your network is going to start by trying these passwords. Also avoid using passwords that contain anything someone could learn with a simple Google search. For example, your dog’s/pet’s name is not a password. Think of it like this—have you ever posted a picture and/or the name of your dog/pet on your social media page? Because, if you have, then it can be found with an online search engine (no matter what kind of security settings you may have on your profile).
Don’t believe me? Try it. Google your name in quotation marks. You might be surprised how anyone with an internet connection can learn plenty of info about you.
 Creating a unique password is fairly simple. Most people know that a strong password is generally considered to have at least six characters and contains at least one letter, one number, and one symbol. However, even this isn’t foolproof. For example, if your last name is Jameson, it isn’t too smart to make your password J@mes0n. Again, this is the kind of password hackers will try. To be honest, just avoid using your names altogether. If you can’t seem to come up with a strong or unique password on your own, consider using a good online password generator to create one for you. I would suggest using Norton-Symantec’s free password generator, as it has already been well vetted and is considered top notch.
Creating a unique password is fairly simple. Most people know that a strong password is generally considered to have at least six characters and contains at least one letter, one number, and one symbol. However, even this isn’t foolproof. For example, if your last name is Jameson, it isn’t too smart to make your password J@mes0n. Again, this is the kind of password hackers will try. To be honest, just avoid using your names altogether. If you can’t seem to come up with a strong or unique password on your own, consider using a good online password generator to create one for you. I would suggest using Norton-Symantec’s free password generator, as it has already been well vetted and is considered top notch.
2. Password Sharing
The second serious (yet frighteningly common) password security mistake is password sharing. A user can have the strongest, most unique password in all existence, but it won’t make a lick of difference if he or she tells it to someone else. Think of the kind of damage that could be done by just one disgruntled former employee who still has a valid password. Sure, you removed their credentials from the system. However, this doesn’t do much good if he or she has the password of someone else who still has access. The best way to deal with this issue is to implement a strict office policy that forbids any of your staff from sharing their passwords, even with fellow employees. Interoffice relationships can be friendly and trusting, but that trust should not include password sharing. Relationships can change, and trust can be betrayed (the NSA agents who shared their credentials with Snowden likely considered him trustworthy).
3. Changing Passwords Regularly
The third method for strengthening password security is to make sure that everyone changes their office passwords regularly. This way, even if someone accidentally shares or learns a password, it will only be for a limited period. At minimum, it’s a good idea to require all office passwords to be changed every 6 months. Changing passwords every 90 days would be even better. As mentioned in Part 1 of this blog series, it’s important to trust your instincts. If you feel that one or more office passwords might be compromised, even if you can’t explain why, you should go ahead and have everyone change their passwords. Doing so definitely won’t do any harm, but doing nothing just might.
Thanks for reading Part 2 of this blog series. In Part 3, we will examine two separate data breaches—at both the 2013 G20 Summit and the Department of Defense. These incidents can teach us a lot about the kinds of potential cyber-threats that can be posed by USB drives and other portable storage devices.